A critical remote code execution (RCE) vulnerability (CVE-2025–27364) has been identified in all versions of MITRE Caldera prior to commit 35bc06e, exposing systems to potential compromise via unauthenticated attackers.
The flaw resides in the dynamic compilation mechanism of Caldera’s Sandcat and Manx agents, which are reverse shells designed for red team operations.
Exploitation requires only the presence of Go, Python, and gcc—dependencies inherently needed for Caldera’s functionality—making the vulnerability virtually universal across default deployments.
The vulnerability was discovered and reported by security researcher Dawid Kulikowski through MITRE’s coordinated disclosure process.
Vulnerability Origin in Dynamic Compilation
The Sandcat and Manx agents rely on Caldera’s dynamic compilation endpoint (/file/compile) to generate implants tailored to operational parameters such as communication protocols and encryption keys.
These parameters are injected via HTTP headers during agent retrieval. Crucially, the endpoint lacks authentication, allowing unauthenticated access to its compilation logic.
MITRE Caldera Team reports that the vulnerability stems from improper handling of user-controlled linker flags (ldflags) passed to the compile_go() function.
While Caldera developers used subprocess.check_output() without shell=True—a practice that typically mitigates command injection—the attack surface extended into linker flag manipulation.
Specifically, the -extld and -extldflags parameters in Go’s linker toolchain enabled indirect command execution via GCC’s -wrapper option.
Exploitation via Linker Flag Manipulation
Attackers bypassed traditional command injection defenses by abusing the Go linker’s -extld flag to specify gcc as the external linker and -extldflags to inject the -wrapper parameter.
This GCC feature allows arbitrary command execution by wrapping subprocess calls with a user-defined binary and arguments.
The -wrapper directive routes all GCC subprocesses through Python, executing the attacker’s code while preserving legitimate compilation flow to avoid detection.
Proof of Concept (PoC)
The following curl command demonstrates exploitability by triggering a reverse shell on the Caldera server:
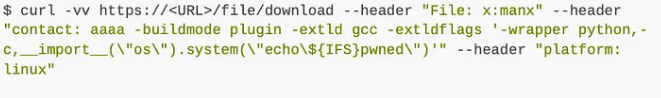
Successful exploitation results in the Caldera server executing the embedded Python script, granting attackers a reverse shell with root privileges.
Mitigation and Recommendations
MITRE has issued an urgent advisory recommending the following actions:
- Update Caldera to v5.1.0 or later, which restricts linker flag modifications and validates compilation parameters.
- Isolate Caldera servers from sensitive environments to limit lateral movement.
- Remove unnecessary build tools (e.g., GCC) from production systems where Caldera operates.
Hence, organizations leveraging Caldera for training or testing should audit their instances for signs of exploitation, including unexpected processes or network connections originating from Caldera hosts.




